Security in IoT Devices: Challenges and Solutions
Anything connected to the internet is likely to face an attack at some point. Attackers may try to remotely compromise IoT devices to steal data, conduct DDoS attacks, or try to compromise the rest of the network. IoT security demands an integrated approach that covers the entire device lifecycle, from design and development to deployment and maintenance.
Security in IoT devices is a primary concern for customers and device manufacturers alike. To ensure secure communication between two devices, there are two key areas that need to be secured. The first is the pipe between the two devices and the data that flows within these channels. This is taken care of by communication protocols like Thread, Bluetooth, etc. The second is the security of the device itself, which is the responsibility of the developer.
There are several standards and frameworks that aim to provide guidelines and best practices for IoT security, such as the IoT Security Foundation, the NIST Cybersecurity Framework, the ISO/IEC 27000 series, and the OWASP IoT Top 10. However, there is no single universal standard that applies to all IoT devices, as different devices have different security requirements and challenges depending on their use cases, functionalities, and environments.
Therefore, IoT device manufacturers and developers need to adopt and implement the standards and frameworks most relevant and suitable for their specific devices and keep up with emerging trends and technologies in IoT security.
While security threats in IoT devices can be low-risk, others can be high-impact and cause considerable damage.
Let us take a dive into the most common IoT security threats.
Unauthorized Access
One of the most common security threats is Unauthorized access. Hackers can gain access to IoT devices through weak passwords and other vulnerabilities, allowing them to control the device or steal personal information. This can include accessing the device's camera or microphone or using the device to launch DDoS attacks.
Data Breaches
Another common security threat for IoT devices is data breaches, which occur when an attacker obtains sensitive or confidential data from the device or its network. This can compromise the privacy and integrity of the data and expose the device or the user to identity theft, fraud, or blackmail.
Malware Attacks
A third common security threat for IoT devices is malware attacks, where malware (normally malicious software) executes unauthorized actions on the victim's system, this can impair the functionality and reliability of the device, and cause damage, disruption, or sabotage to the device or its network.
Distributed Denial of Service Attacks
Another security threat for IoT devices is denial-of-service attacks, DDoS is an attack that targets the availability of resources and servers of a network by flooding the communication medium from distinct locations by using various IoT devices, which makes it harder to detect. Thus, analyzing and defending DDoS is a protruding field of research.
Physical Tampering
This is another threat that occurs when an attacker physically accesses, changes, or damages the device or its components. It can compromise the integrity, functionality, and confidentiality of IoT devices. This can affect the security and functionality of the device, and enable the attacker to access, manipulate, or destroy the device or its data.
How Silicon Labs Addresses IoT Security Challenges
When the subject of security comes up, there is generally a mention of data breaches, malware attacks, denial of service attacks, etc. However, there are some additional attacks that IoT devices are prone to. This can be as simple as an attacker attempting to run their unauthorized code on your device, or attempts to perform product counterfeiting, or complex like differential power analysis attacks.
Silicon Labs addresses these concerns through Secure Vault™. Secure Vault by Silicon Labs is an advanced suite of security features designed to protect Internet of Things (IoT) devices from such evolving threats.
Silicon Labs is a leading provider of silicon, software, and solutions for IoT devices, with a focus on delivering secure and reliable connectivity for a smarter, more connected world, offers a robust and comprehensive portfolio of IoT security products and services with features like secure boot, secure debug, secure key management, and secure identity.
Let us look at the prevalent security countermeasures that can help protect the end-device secret and private keys and ensure a completely secure ecosystem.
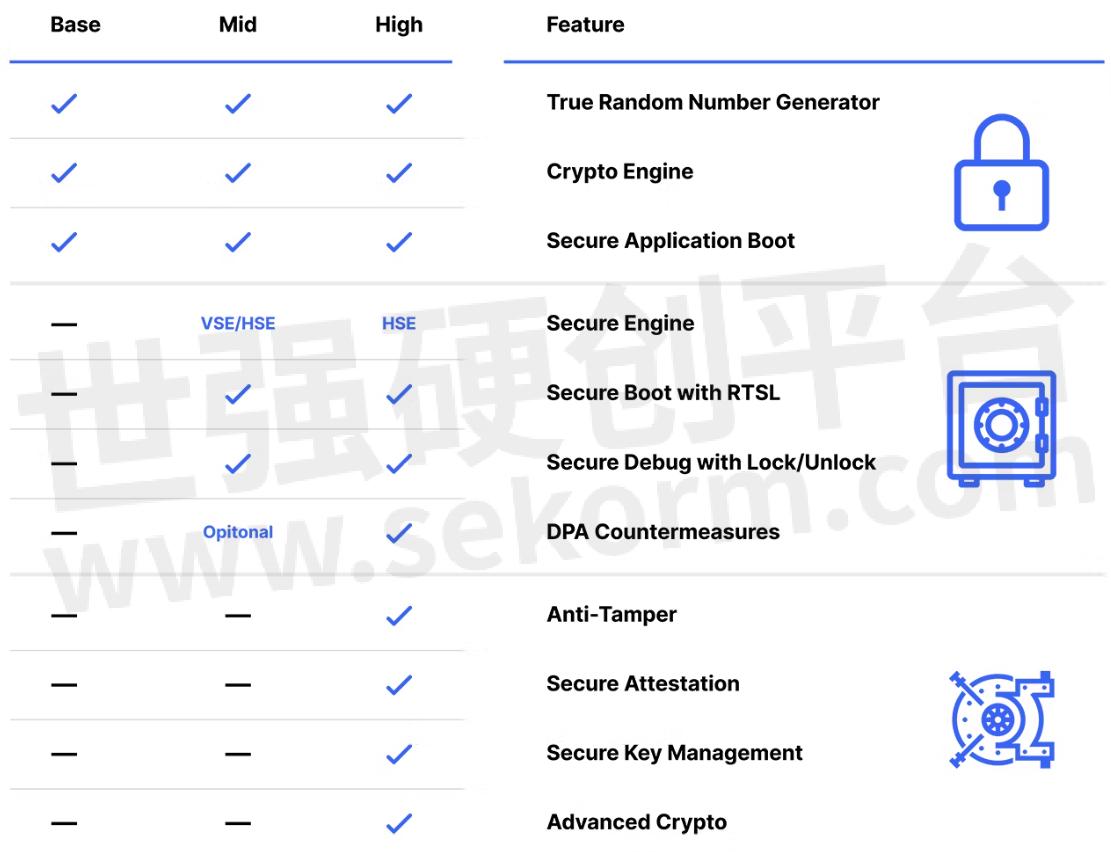
Secure Vault Mid features will protect end-devices from logical attack vectors. Applications that also require protection against physical attack vectors will require Secure Vault High features such as secure key management and tamper protection. Device manufacturers looking to protect their devices from product counterfeiting as well as cloning of devices should consider investing in secure identity, which enables commissioners to authenticate the identity of the device before allowing it to join the smart IoT network.
Secure Key Mmanagement
There are various methods for storing keys securely. One method is to create very expensive memory cells that are buried into a security subsystem. These memory cells are expensive from a silicon die area perspective, and there is always the important decision: How many do we put in the chip? Ultimately, there are never enough cells and some key material ends up being stored unencrypted in plaintext in standard memory. Another method for secure key storage is to use a Physically Unclonable Function, or a PUF, to create a device-specific Key Encryption Key and store all key material in encrypted Key BLOBs in standard memory. This has the additional benefit of giving you almost unlimited secure key storage.
Physically Unclonable Function (PUF)
A PUF is a physical structure embedded in an integrated circuit (IC) that is very hard to clone due to its unique micro- or nano-scale properties originating from inherent deep-submicron manufacturing process variations. The static random access memory (SRAM) PUF is the best-known PUF based on available standard components.
Other Attack Vectors
There is always a threat of an attacker attempting to run their unauthorized code on our device, Secure boot addresses this concern by validating the signature on the application code before allowing it to run on the device. This is based on a ROM-based Root of Trust that serves as a secure anchor for the verification sequence. We can also prevent unauthorized access to the device by locking the debug port and by enabling DPA countermeasures to protect the device from being unlocked through side-channel attacks.
Security is a very interesting aspect of IoT devices as one can never ensure 100% protection against it. Just like more layers make it difficult to peel an onion, the more layers we create in a device, the harder and more expensive it becomes for an attacker to access the information. We at Silicon Labs, follow a security-by-design philosophy, which means that security is embedded and integrated into every stage of the device lifecycle, from design and development to deployment and maintenance.
- +1 Like
- Add to Favorites
Recommend
- Silicon Labs Helping Smart Home Manufacturers Meet IoT Security Regulations
- Navigate the New IoT Labeling Program with Silicon Labs’ Best-In-Class Security
- Silicon Labs‘ Secure Vault Becomes World‘s First IoT Security Solution to Achieve PSA Certified Level 3 Status
- Sillicon Labs‘ Secure Vault Technology Is for Developing Extremely Robust, Secure IoT Wireless Solutions
- Silicon Labs Launches Security Services to Support ‘Zero Trust‘ Security Model in IoT
- Silicon Labs Wi-Fi 6 Solutions Help You Convince Buyers by Designing More Secure Wi-Fi Devices
- Silicon Labs Unveils World‘s First Secure Sub-GHz SoCs With 1+ Mile Wireless Range And 10+ Year Battery Life
- Silicon Labs xG26 Sets New Standard in Multiprotocol Wireless Device Performance
This document is provided by Sekorm Platform for VIP exclusive service. The copyright is owned by Sekorm. Without authorization, any medias, websites or individual are not allowed to reprint. When authorizing the reprint, the link of www.sekorm.com must be indicated.